Fail2ban — is a popular intrusion detection system for Linux. It monitors log files to detect automated attacks and failed login attempts. After identifying the IP address responsible for the intrusion, Fail2ban immediately blocks that IP address. It is very useful for blocking brute-force attacks. Installing and using Fail2ban is fairly simple. Here are the instructions to install Fail2ban on Ubuntu.
- Update Ubuntu
Open a terminal and run the following commands to update your Ubuntu system.
sudo apt-get update sudo apt-get upgrade
-
Install Fail2ban
Follow the command below to install fail2ban.
sudo apt-get install -y fail2ban
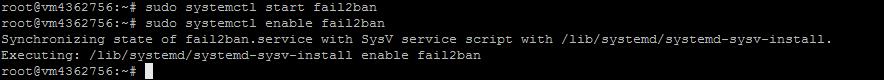
- Activate fail2ban
Start and activate fail2ban with the following commands
sudo systemctl start fail2ban sudo systemctl enable fail2ban
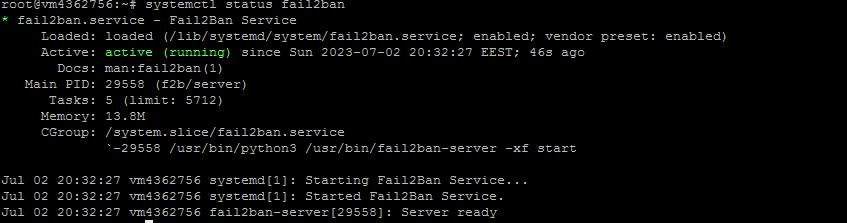
You can check the status of fail2ban with the following command
sudo systemctl status fail2ban
-
Customize Fail2ban
There are 4 configuration files available to fail2ban. It reads these files in the following order:
/etc/fail2ban/jail.conf /etc/fail2ban/jail.d/.conf /etc/fail2ban/jail.local
Ordinary people copy the default jail.conf to jail.local and update it.
We copy the jail.conf file as shown below:
sudo cp /etc/fail2ban/jail.conf /etc/fail2ban/jail.local
Open jail.local with a text editor
sudo vim /etc/fail2ban/jail.local
In this file you will find different sections, each one well commented out about what it does.
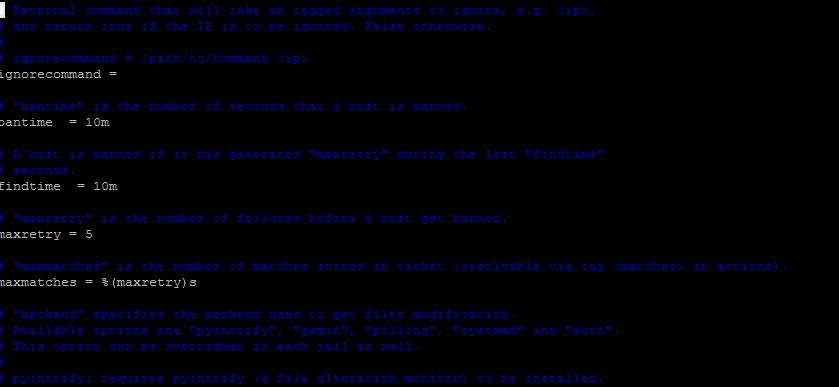
We'll look at some basic settings:
-
ipignore – used to block IP addresses and ranges. To block one or more IP addresses, uncomment the line that starts with ipignore and add IP addresses separated by commas. Here is an example.
ipignore = 127.0.0.1/8 ::1 23.23.23.23 192.125.1.0/24
-
bantime – block duration. The default value is 10 minutes. Here is an example to set it to 1 day.
bantime = 1d
-
findtime – the length of time for the specified number of failures or attacks to occur. If you configured fail2ban to block IPs after 3 failures, they should happen within the findtime value. Here is an example
findtime = 10m
-
maxretry – the maximum number of failures before the IP is blocked. For example,
maxretry = 5
Test and unblock the IP address
Try logging into your server via SSH and fail all attempts by entering incorrect credentials. You won't be able to log in to your server via SSH after the third attempt.
Fail2ban comes with a client that allows you to control its service. You can use it to remove blocking from an IP address.
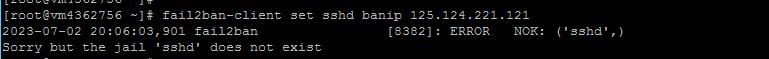
Unlocking an IP address (e.g., 125.124.221.121)
sudo fail2ban-client set sshd unbanip 125.124.221.121
If you get this error fail2ban [7825]: ERROR NOK: ('sshd',), Sorry but the jail 'sshd' does not exist - , this indicates that fail2ban cannot find the 'sshd' configuration. jail" in Fail2ban are rule sets for the various services that Fail2ban should monitor, such as ssh, apache and others.
First, you need to check the Fail2ban configuration file (usually '/etc/fail2ban/jail.conf' or '/etc/fail2ban/jail.local') and make sure it has a section for 'sshd'. It should look something like this:
[sshd] enabled = true port = ssh logpath = %(sshd_log)s backend = %(sshd_backend)s
After making any changes to the configuration file, Fail2ban must be restarted with the command:
sudo systemctl restart fail2ban
The command to block the IP address should now work without errors.
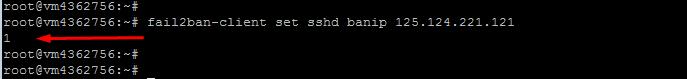
Blocking an IP address (e.g. 125.124.221.121)
sudo fail2ban-client set sshd banip 125.124.221.121
In summary, Fail2ban is an effective intrusion detection system that blocks the IP addresses that make repeated failed login attempts. It plays an important role in keeping your Linux systems secure, whether it's Ubuntu or CentOS 7.
This article will help you install and configure Fail2ban on your servers without any problem. In addition to installing and enabling Fail2ban, you can also learn how to configure IP blocking settings, verify service status, and manage the blocking of specific IPs.
While this system is a powerful tool for defending against automated and brute-force attacks, it's important to remember that Fail2ban should be used in conjunction with other security measures, such as strong passwords, system updates, and activity monitoring, to provide maximum protection.

