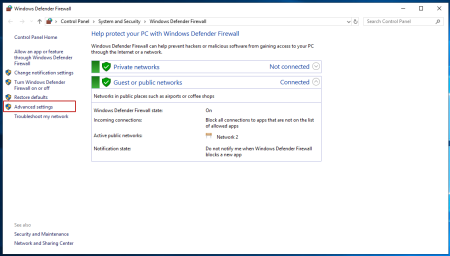
If such programs give an error due to a closed port, then it can be opened using the Windows Firewall snap-in. In the Windows 2012 operating system, right-click on Start and select Control Panel from the context menu. Go to System and Security, then Windows Firewall.
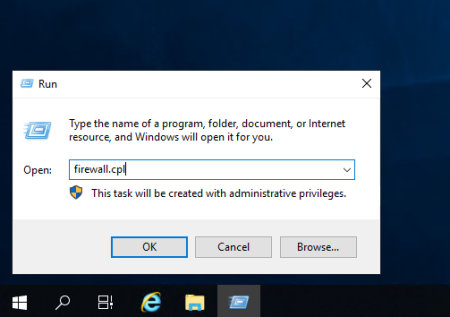
Or, for Windows OS versions 2016 and 2019, you can use the Win+R key combination and enter the firewall.cpl command in the Open window.
In the window that appears, on the left side, click on Advanced Settings and proceed to adding rules.
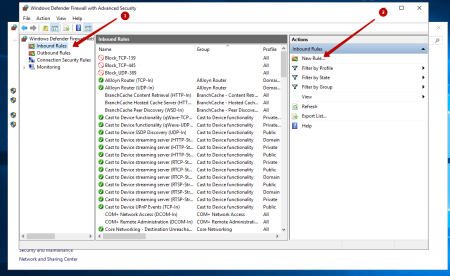
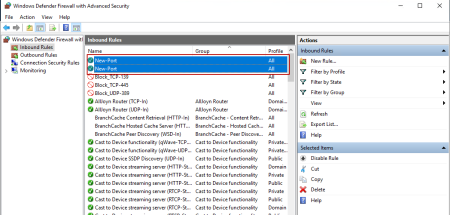
In the new window, on the left side, select the Inbound Rules tab, then on the right side of the window, in the Actions column, select the New Rule item ...
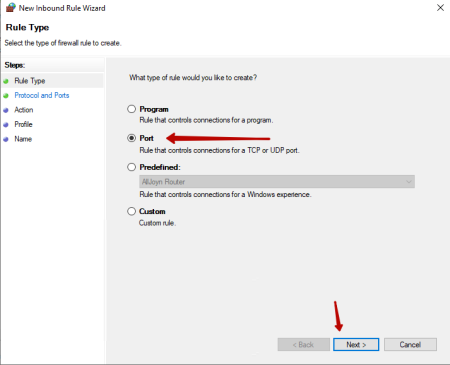
After that, in the New Inbound Rule Wizard window that appears, in the Rule Type item, select the Port value, and click Next.
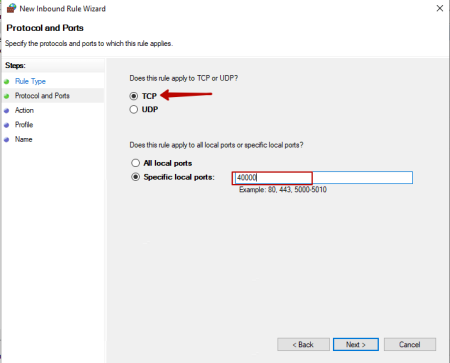
After that, you need to specify the protocol we need, and the port we need. In our case, this is TCP and port 42000. And click Next.
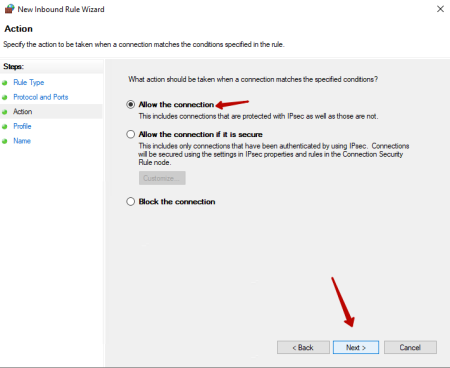
In the next window, select Allow the connection and click Next.
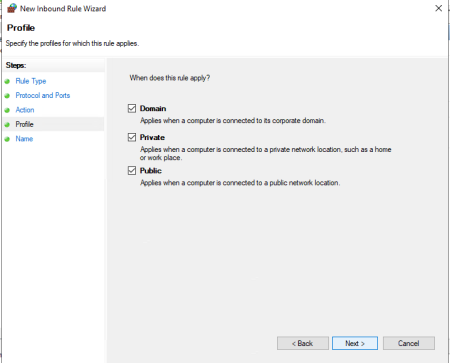
In the Profile item, mark the required firewall profiles and click Next.
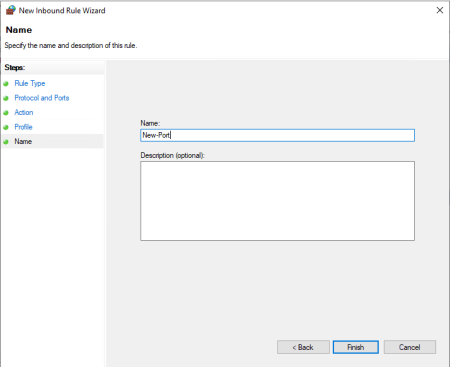
In the last Name window, enter a name and if you need a description for this rule, and click Finish.
Now you need to add UDP in the same way. On the left side, select the Inbound Rules tab, then in the right part of the window, in the Actions column, select the New Rule item ... And so on according to the instructions.
If you need to add a range of ports, they can be added with a dash.
For example: 40000-41000
Now we can observe the added rules in the list of rules for incoming connections.
After launching an application that uses the ports that you have added, it should start without errors.
You can also use PowerShell for this and spend less time.
For example, we can use the port 40000.
For TCP protocol:
netsh advfirewall firewall add rule name="New-Port" protocol=TCP localport=40000 action=allow dir=IN;For UDP protocol:
netsh advfirewall firewall add rule name="New-Port" protocol=UDP localport=40000 action=allow dir=IN;By the same analogy, you can open the necessary ports.

